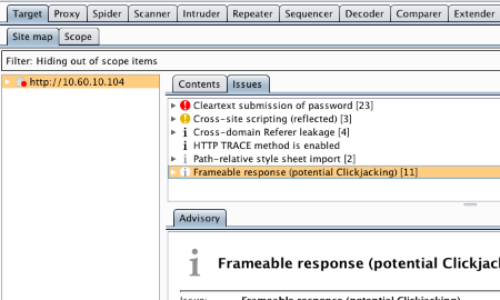
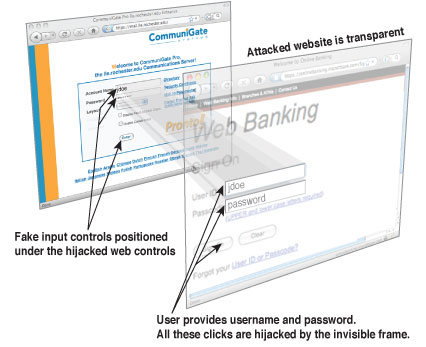
CSP frame-ancestors vs. X-Frame-Options for Clickjacking prevention · RapidSec - CSP and Security Headers Made Easy

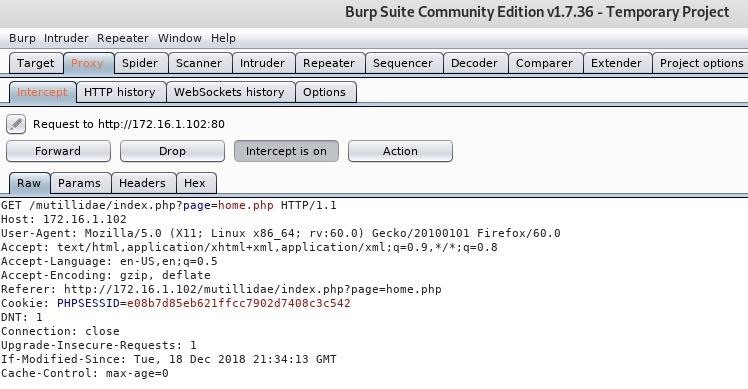
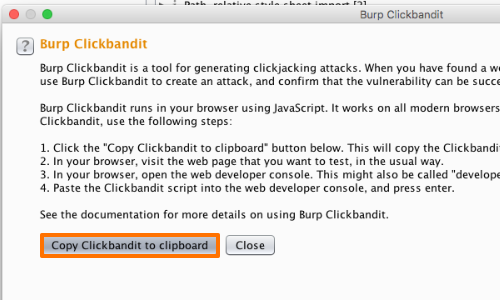
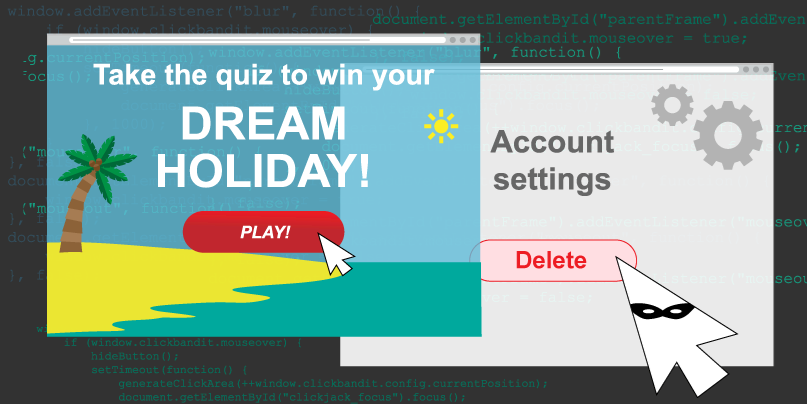
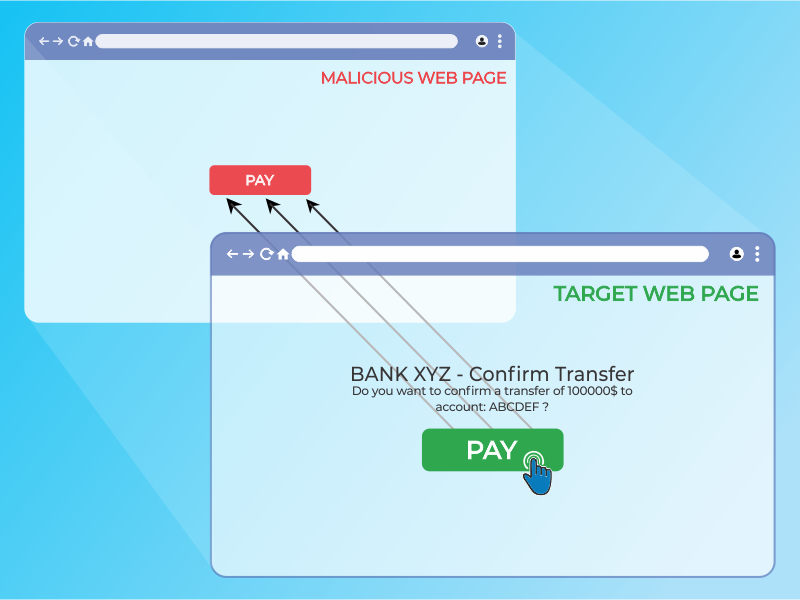
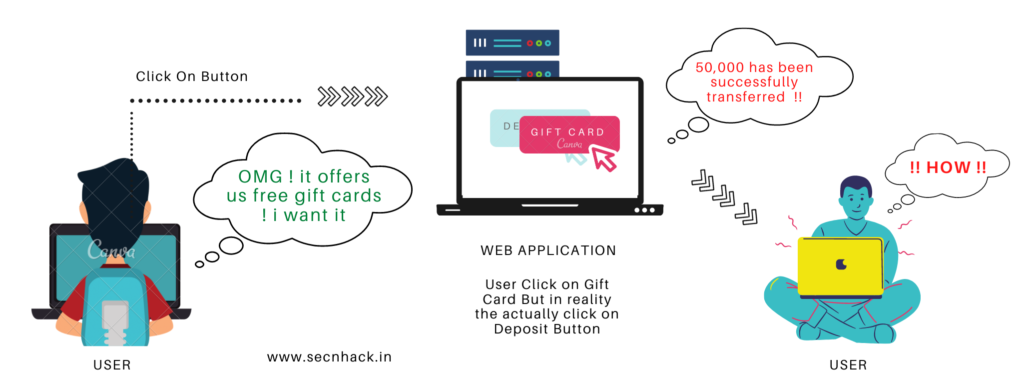
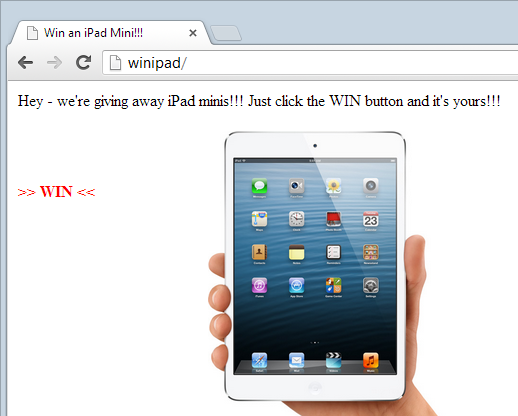
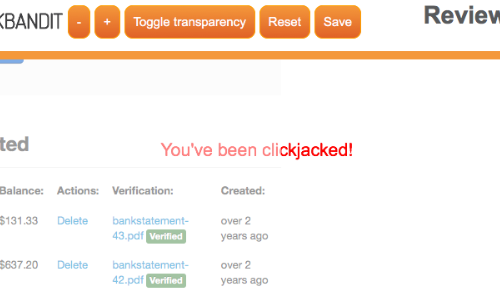
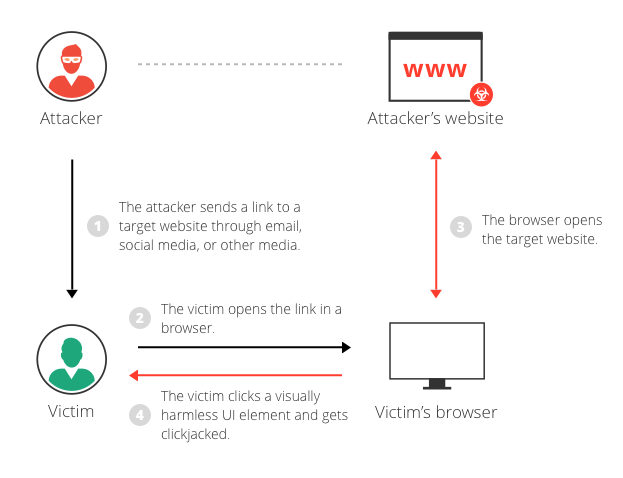
NMAS Click Jack Security Vulnerability: X-Frame-Options or the Content-Security-Policy's frame ancestor option missing to prevent Click Jacking attacks