Scanning an enterprise organisation for the critical Java deserialization vulnerability | Weblog | Sijmen Ruwhof

Burp Suite on Twitter: "@damian_89_ The extension settings are saved in a local config file and should persist on a restart. How many extensions do you have loaded?" / Twitter

Java-Deserialization-Scanner – BurpSuite JAVA deserialization vulnerability scanning plug-in – Penetration Testing | Julio Della Flora

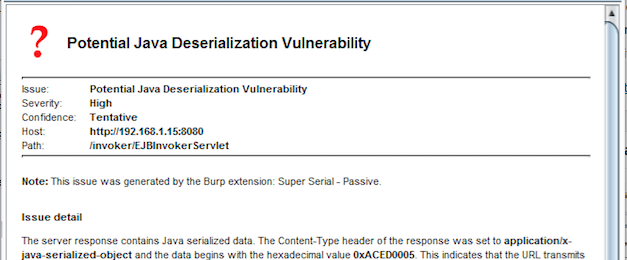
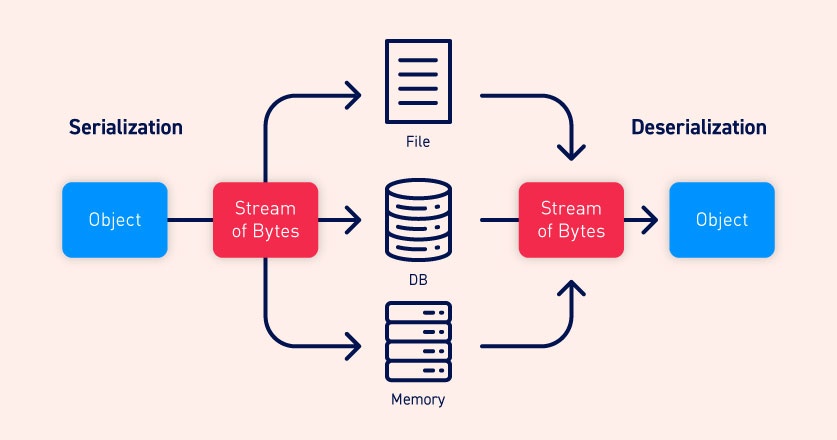
Reliable discovery and exploitation of Java deserialization vulnerabilities | @Mediaservice.net Technical Blog
GitHub - PortSwigger/java-deserialization-scanner: All-in-one plugin for Burp Suite for the detection and the exploitation of Java deserialization vulnerabilities

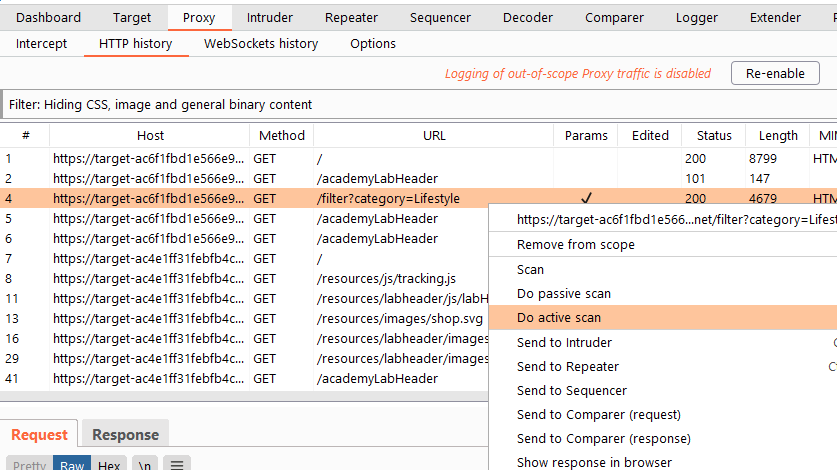
Extracting data using Insecure Direct Object Reference (IDOR) flaws | Hands-On Application Penetration Testing with Burp Suite

Java Deserialization — From Discovery to Reverse Shell on Limited Environments | by Francesco Soncina (phra) | ABN AMRO — Red Team | Medium

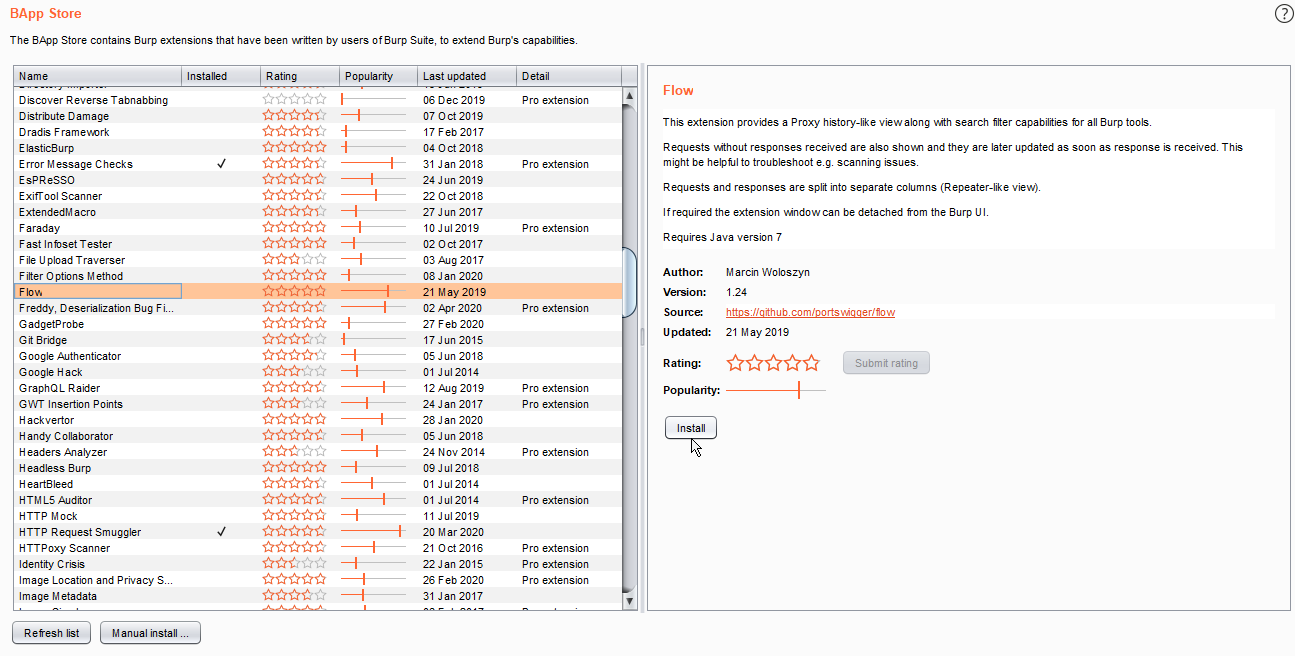
![Java Deserialization Scanner - Hands-On Application Penetration Testing with Burp Suite [Book] Java Deserialization Scanner - Hands-On Application Penetration Testing with Burp Suite [Book]](https://www.oreilly.com/library/view/hands-on-application-penetration/9781788994064/assets/2d7c668b-0b42-4198-81a7-764164a9b945.png)
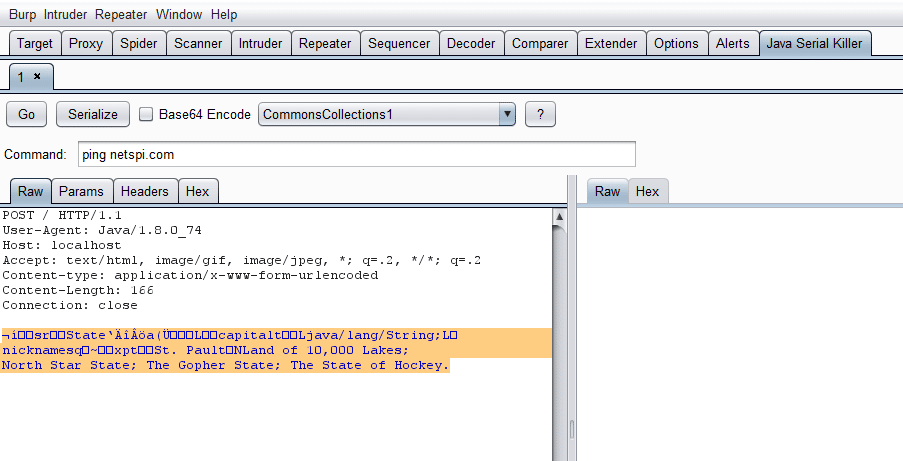
![Java anti sequence scanning tool] introduction, download, installation and use Java anti sequence scanning tool] introduction, download, installation and use](https://img.inotgo.com/imagesLocal/202204/22/202204222153505876_4.png)
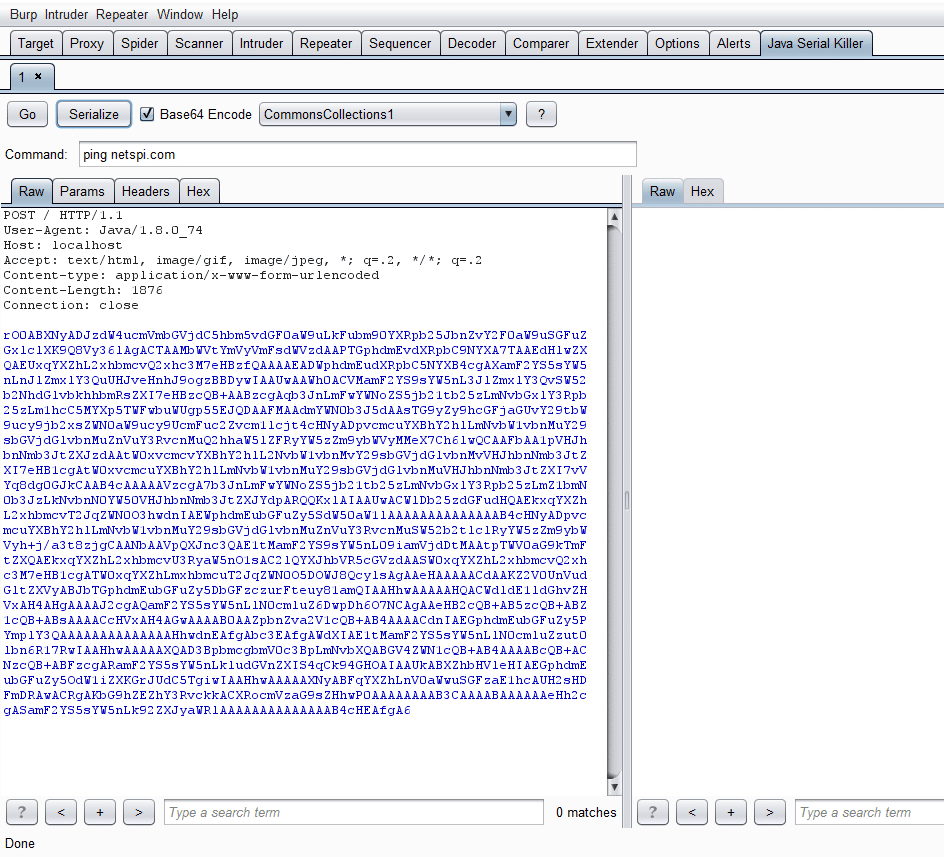

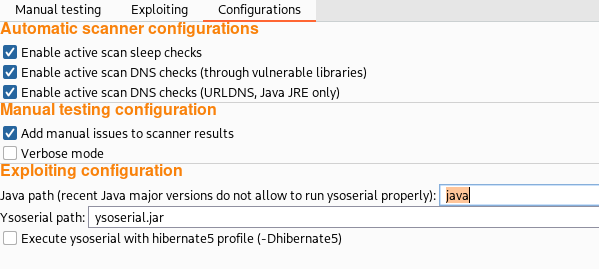

![Java Deserialization Scanner - Hands-On Application Penetration Testing with Burp Suite [Book] Java Deserialization Scanner - Hands-On Application Penetration Testing with Burp Suite [Book]](https://www.oreilly.com/library/view/hands-on-application-penetration/9781788994064/assets/21233bba-91ba-4033-86c3-f7f7bb722b23.png)